Security in DevOps Best Practices to Keep Your Pipeline Secure

Software development, DevOps practices have become a cornerstone for organizations looking to streamline their processes and deliver high-quality software. While the agility and efficiency DevOps brings to the table are undeniable, it’s essential to remember that security should never be compromised in the pursuit of speed. In fact, it should be an integral part of the entire DevOps lifecycle. In this blog, we’ll delve into the best practices for maintaining security in your DevOps pipeline.
Implement Security as Code
Just as you write code to build and deploy applications, security should be treated as code. Security as Code involves integrating security checks and measures directly into your DevOps pipeline. Tools like Infrastructure as Code (IaC) and Security as Code (SaC) can help automate security practices, making them an integral part of your development process.
Conduct Regular Security Assessments
Regular security assessments, such as penetration testing and vulnerability scanning, should be conducted throughout the development process. These assessments identify potential security vulnerabilities, ensuring that issues are addressed before they reach production.
Container Security
Containers are widely used in DevOps for their scalability and portability. To secure your containers, employ container security tools that scan for vulnerabilities, limit the attack surface, and enforce security policies within containers.
Start with a Security-First Mindset
The first and most crucial step to secure your DevOps pipeline is to embed a security-first mindset into your team’s culture. Ensure that security is considered from the initial stages of development and remains a top priority throughout the pipeline. By integrating security into your DevOps process from the beginning, you reduce the likelihood of vulnerabilities slipping through the cracks.
Continuous Monitoring and Testing
Regular security testing is essential to detect and fix vulnerabilities early in the development process. Incorporate automated security scanning tools into your pipeline for continuous monitoring. Static application security testing (SAST) and dynamic application security testing (DAST) are two common methods used to identify security flaws in code and application behavior.
Version Control and Code Review
Effective version control and code reviews are crucial components of a secure DevOps pipeline. Ensure that your code repositories are secure, and all code changes are reviewed by peers. Tools like Git and platforms like GitHub provide features that facilitate these practices while maintaining code integrity.
Infrastructure as Code (IaC) Security
As infrastructure as code becomes more prevalent, it’s vital to focus on the security of your IaC scripts and configurations. Utilize security-focused IaC tools to scan and validate your infrastructure code to prevent misconfigurations and vulnerabilities that could compromise your environment.
Secure Credential Management
Never hardcode credentials, tokens, or keys into your code. Utilize a secure secrets management solution like HashiCorp Vault or AWS Secrets Manager to store and access sensitive information securely. This ensures that secrets are never exposed in your codebase or during the deployment process.
Access Control and Least Privilege Principle
Implement strict access controls and adhere to the principle of least privilege. Only grant access and permissions to individuals who genuinely require them. Utilize role-based access control (RBAC) and ensure that permissions are regularly reviewed and revoked when no longer necessary.
Regular Updates and Patch Management
Stay current with updates for all components in your DevOps pipeline, from operating systems to third-party libraries and software. Unpatched vulnerabilities are low-hanging fruit for attackers, and regular updates are your first line of defense against known security flaws.
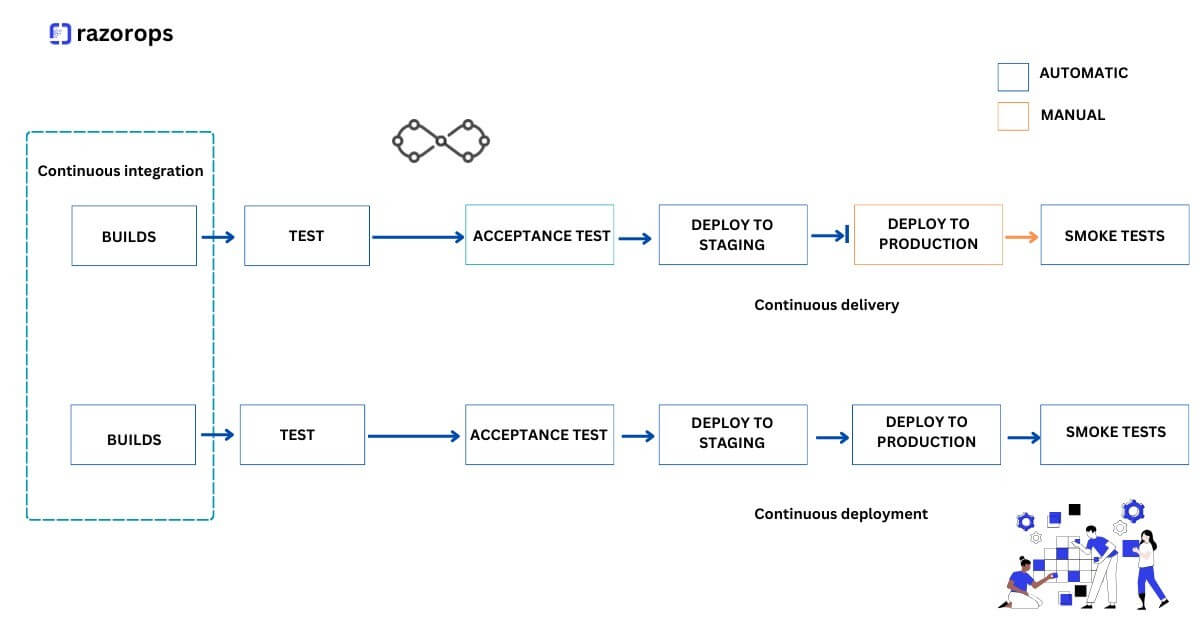
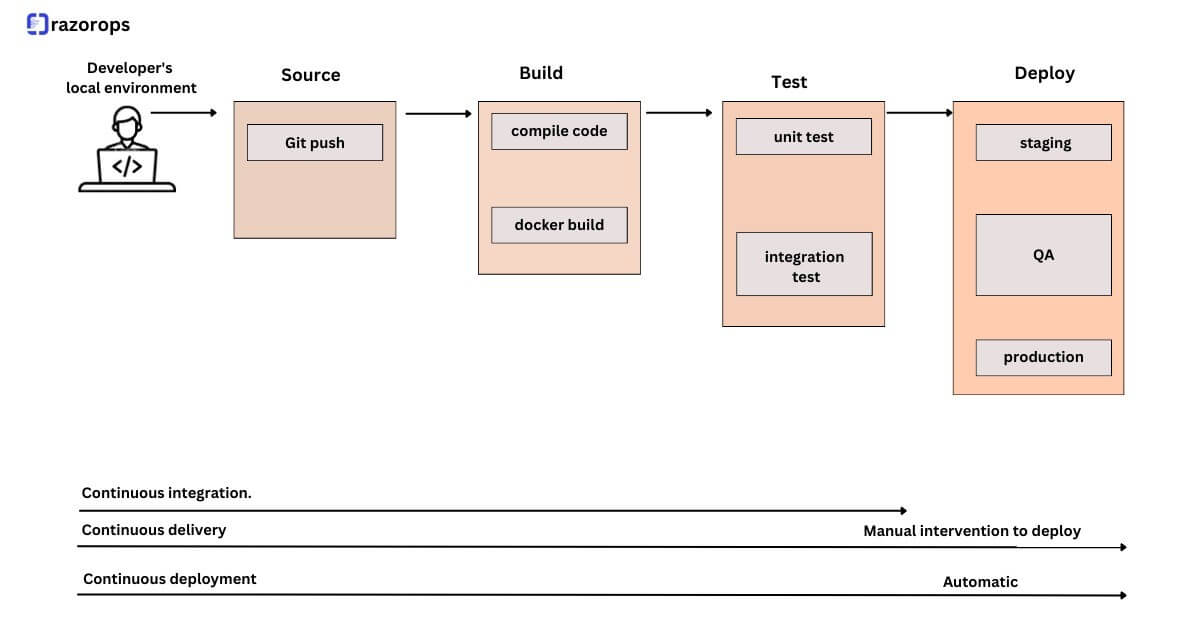
Secure CI/CD Pipeline
The Continuous Integration and Continuous Deployment (CI/CD) pipeline itself should be secure. This includes securing build servers, code repositories, and ensuring that only trusted artifacts are deployed to production. Implement strong access controls and monitoring for your CI/CD tools.
Incident Response Plan
No matter how diligent you are, security incidents can happen. Prepare for the worst by having a well-defined incident response plan in place. This plan should outline how to detect, respond, and recover from security breaches swiftly.
Security in DevOps is not an afterthought; it’s an integral part of the entire software development lifecycle. By incorporating these best practices into your DevOps pipeline, you can mitigate risks, protect your organization, and deliver secure, high-quality software more efficiently. Remember that security is an ongoing commitment, and staying vigilant is the key to a resilient DevOps security strategy.